Hunt or Be Hunted: How to Avoid a Personal Data Breach
Carson Malapit never thought it would happen to her.
Malapit had been trying to login to her LinkedIn account, and realized she could not get access. Now, the social media she used to network with professionals was under someone’s control – she had been hacked.
“I thought my career was ruined,” said Malapit, a student from Indiana University.
Job-hunting has become a predominately online expedition, which is quite alarming, considering the personal information disclosed during the process. About 64 percent of Americans have experienced a personal data breach, and relatively large shares of the public lack trust in key institutions to protect their personal information, according to Pew Research Center. With this in mind, here are three ways to take your cyber-security into your own hands while trying to score that next gig.
Don’t Trust Third-Parties
While it may come as no surprise that third party companies are susceptible to data breaches, it is common to use services that aggregate job listings (i.e. Monster, Indeed). While these may prove useful, it is more beneficial to use them for finding listings, then checking if the employer’s website will let you apply directly, said Frank Breitinger, professor and co-director of the Cyber Forensics and Education Group at the University of New Haven.
“The first thing I do is analyze the website…Why am I submitting my data to a third party? I would not register my information with third parties.”
Your Friend, VPN
If you find yourself traveling often, working frequently in public spaces or using Internet connections you are wary about, you may want to consider using a virtual private network, or VPN. A VPN is a way for you to connect to a private encrypted network, even in a public setting – they are essentially like a mask for your computer, according to an article from Gizmodo. With it, you could access secure documents from a home computer from anywhere in the world.
“For more common places, I don’t leave my network unencrypted. Whenever you’re in a popular place, it’s just a good idea,” said Breitinger.
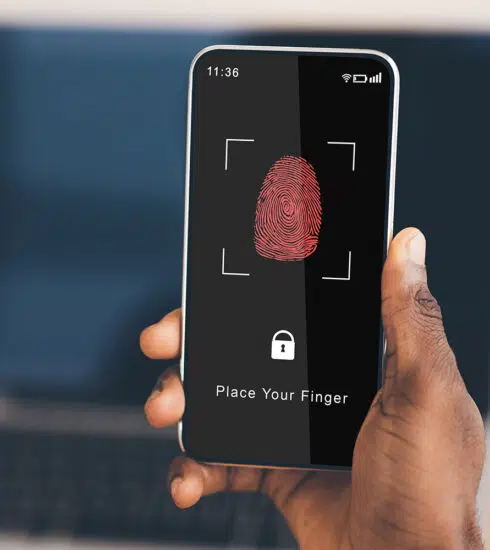
Two-Factor Verification
With the growing popularity of the Internet of Things (IoT) and the interconnectivity of devices, securing sensitive documents for employers has never been easier. You may not know it, but you use two-factor verification (authentication) (2FA) in your everyday life – for example, your bankcard (factor one) and your pin (factor two), according to an article from TechTarget.
Apps such as Duo provide two-factor verification, and typically have a free version for a certain number of users. For less than the cost of your Netflix account – six dollars a month – you are allowed access to more forms of verification, and can extend your subscription to multiple devices. If you adopt the technology now, you may be ahead of the curve as an early adopter, according to Jessica Robinson, CEO of PurePoint International, a boutique security firm that specializes in cyber technology solutions and risk assessment.
“I’d like to think in the next five years we’ll get rid of passwords. [Multi-factor authentication] will be compliant across different industries,” said Robinson.
Malapit, during her ordeal, adopted two-step verification across all of her social media,
“You need to do it. I tell everyone to use two-step verification. It’s so easy,” said Malapit.
“Should I Have Posted That?”
This last tip may seem obvious, but it’s worth noting. The permanence of the Internet is not to be tampered with, yet we forget this when making posts on our favorite social media. The same logic applies to our professional documents as well, according to Robinson.
“Be careful where you put your resume. Limit the amount of [personal] information you put out,” said Robinson.
You should never include your Social Security number or any information that could be linked to your financial affairs. With social media such as Facebook and Snapchat offering users the ability to send money via through instant messages, it is increasingly easier for hackers to gain access to important information. Jamie Kendrick experienced a hack of this nature.
“[The hacker] made small charges to my account. If you get any sort of call that your credit card information is compromised, you need to change all of your [media] accounts,” said Kendrick, an Indiana University graduate.
After months without her social media accounts, failed attempts to work with law enforcement to recover them and contacting past and future employers to explain the nature of the hack, Malapit got her accounts back.
“You hear about stuff like this all the time, but you don’t think it will happen to you. It’s so easy…just like that, I [was] hacked. “